“The CFP for #Bsides #Stuttgart is Open! Please submit your presentations, workshops, demonstrations, etc. There will be a track dedicated to #AutomotiveSecurity from #ASRG https://t.co/7hQ3JFfuO7”
Tag: CarHacking
4CAN V2
4CAN V2 is a Raspberry Pi project created by the Cisco team in order to test the security of cars via the 4CAN bus, it can also send random payloads to automate this process.
Hm… much bling but should keep 4CAN V2 on the radar:
Vehicle Spy Workshop
Participated at the workshop Vehicle Spy with Intrepid by the Automotive Security Research Group at Shackspace (Stuttgart) and really liked it (despite me looking asleep all the time due to critical caffeine levels).
TIL: Don’t attack the crypto. Attack the implementation.
KW902 ODB2 Dongle In Detail
Picked my KW902 apart today to see what’s inside. It features probably a SN65HVDA1050A CAN tranciever (ISO 11898-2 high speed up tp 1 Mbps) a BK3231S SoC for Bluetooth 3.0 and 4.0 programmable via JTAG/FLASH both controlled by a PIC18F25K80 (cheapest of the family, also up to 1Mbps bit rate, comforms to CAN 2.0B) programmable via ICSP.
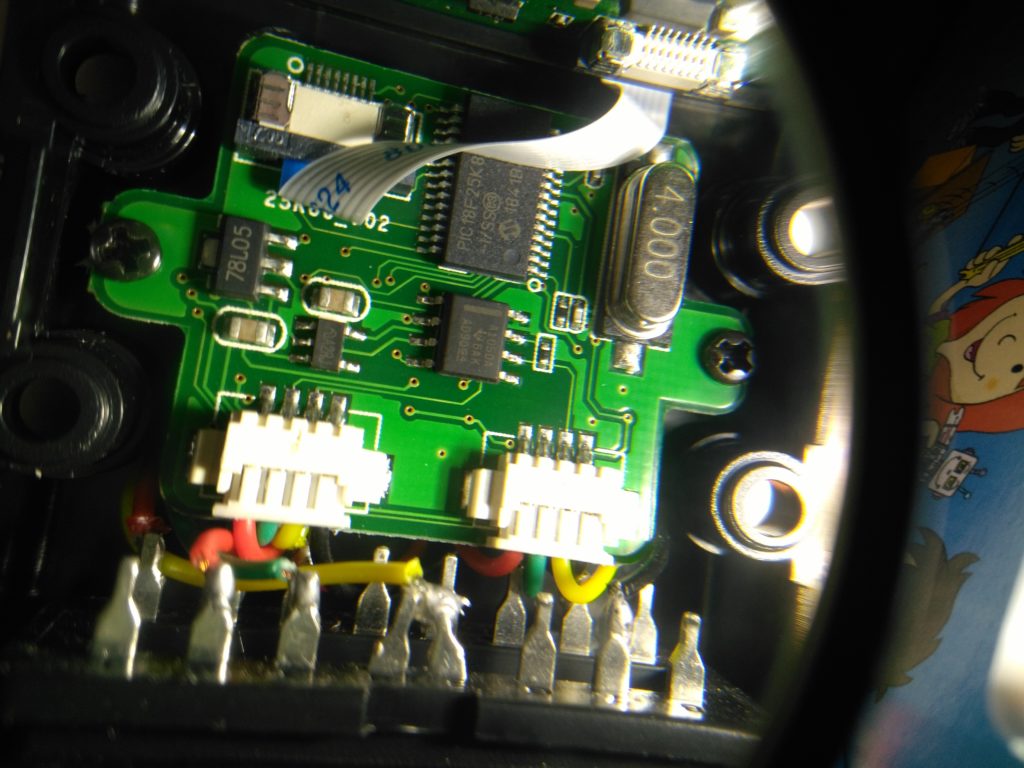
The pins for ICSP may be exposed on the cable for the LED and RST button but since I don’t have the equipment to read out the firmware I didn’t look too closely and called it a day – for now. This cheap IC costs ~2 EUR btw and is well documented.
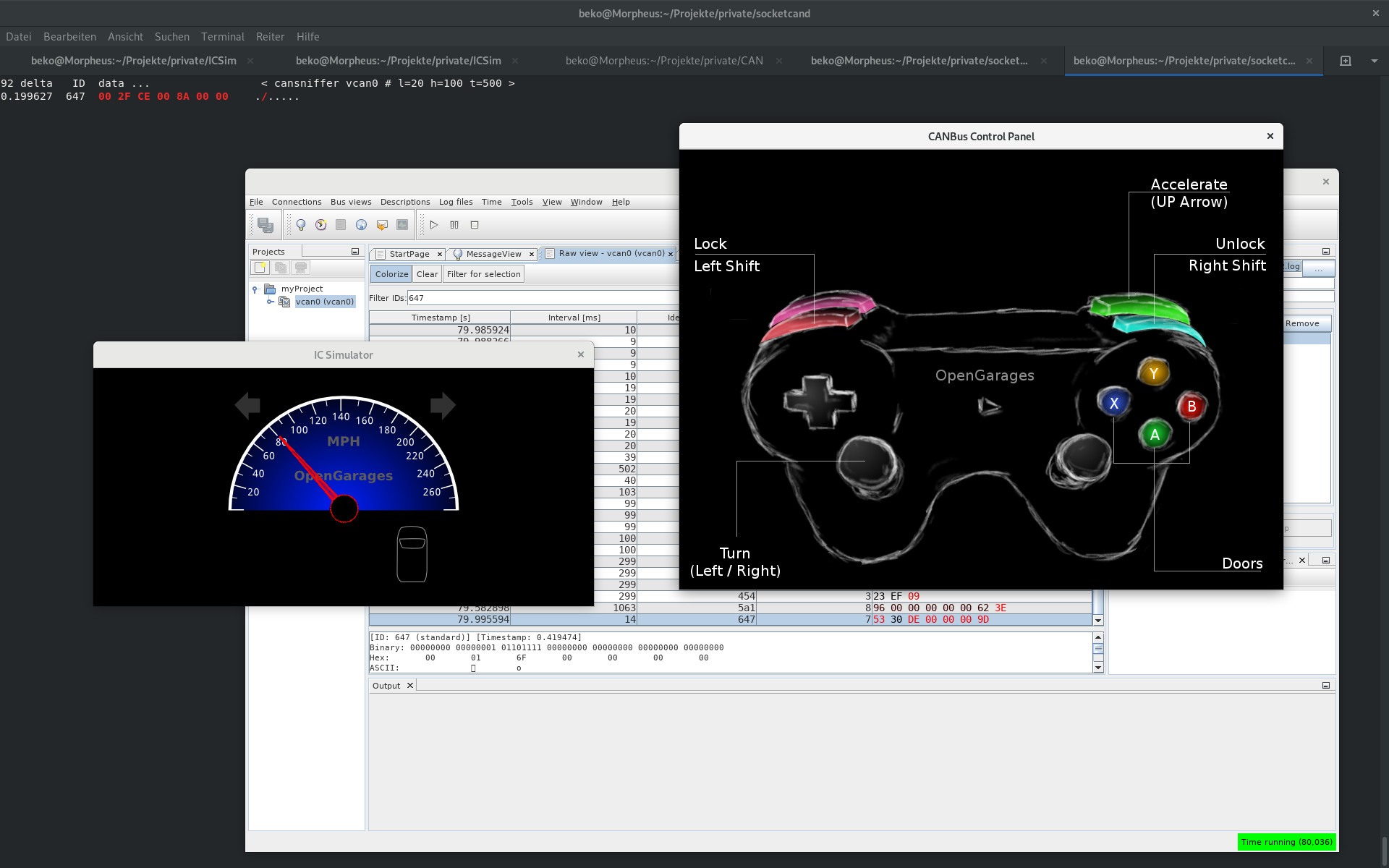
Learning CAN
Making use of ICSim and cansniffer (and Kayak) to learn more about CAN. This is more fun than expected 🙂
Learning Car Hacking
I also learned a damn lot about ODBII, CAN communications, CAN bus transceivers and ECU files. And I found this book for my Read Later bin:
“Car Hacker’s Handbook: A Guide for the Penetration Tester”
ISBN-13: 978-1-59327-703-1

